Malware Analysis has evolved rapidly. Automated sandboxes like ANY.RUN and scanning giants like VirusTotal are now part of every analyst’s toolbox. However, amidst this growth there is a question which has been surfacing online:
“Do we need malware analysts anymore”
Now, this question is fair but the answer is simple:
“Yes. We need malware analysts more than ever”
And in this article, I’ll prove and clarify this using real and safe lab examples.
Why Does this MYTH Exist?
Tools like VirusTotal and ANY.RUN have been very helpful recently and does a very great job at providing what has happened.
They will provide you with:
- Behavioral visuals
- Static scanning
- AI based tags
- Family classification
- Network visibility
- Threat Intelligence Feeds
So here’s what people started to think:
“Why analyze manually? The tool already knows it”
But the reality is:
“Tools can only see. ANALYSTS can UNDERSTAND”
And the different between the two is massive.
Sandboxes sees the behavior. Analysts sees the intent
Let us understand this with a very simple example. A malware with ability to start a child process, drop a file and making a connection is shown as malicious in ANY.RUN. But it can’t tell you the hidden logic behind it. The malwares these days have the ability to even bypass these sandboxes and not run on them.
Let me explain with an example: A malware is made to run only if certain conditions are met.
- Username ≠ “lab”
- And system if online for 3+ hours
- And mouse moves at least 200px
When put in ANY.RUN, it will look like a clean file.
A human reverse engineer will find the conditions in the code and bypass them.
Modern Malwares detects VT & ANY.RUN and refuses to even execute on them
Tools like ANY.RUN and VirusTotal aren’t exclusive to malware analysts or defenders. Attackers are aware of these common tools and sandboxes and they use it to their advantage as well.
So a malware will:
- Sleep for 6+ hours
- Crash inside a virtual environment
- Hide payloads unless a real user interacts with the system
- Stop execution if it detects “VirusTotal” environments
Example:
A recent infostealer malware refused to unpack unless:
- CPU > 4 cores
- Webcam Detected
- Battery Present ( laptop )
For the above, ANY.RUN shows nothing, a reverse engineer discovers everything.
VirusTotal gives signatures, not understanding
So lets say you upload a malware on virus total, you will get a lot of things like:
- IOCs
- Dropped Files
- Threat Intelligence
- What engines detects it
But it can’t tell you:
- What data it steals
- Whether the C2 server is still active or not
- How to detect it in your network
- How to properly write YARA/SIGMA rules
Example:
A banking trojan on VT may show: “Generic.Malware.1234”
A malware analyst can properly tell:
“This exfiltrates clipboard data, harvests cookies, uses RC4 encryption, and communicates via HTTPS to a hidden PHP panel.”
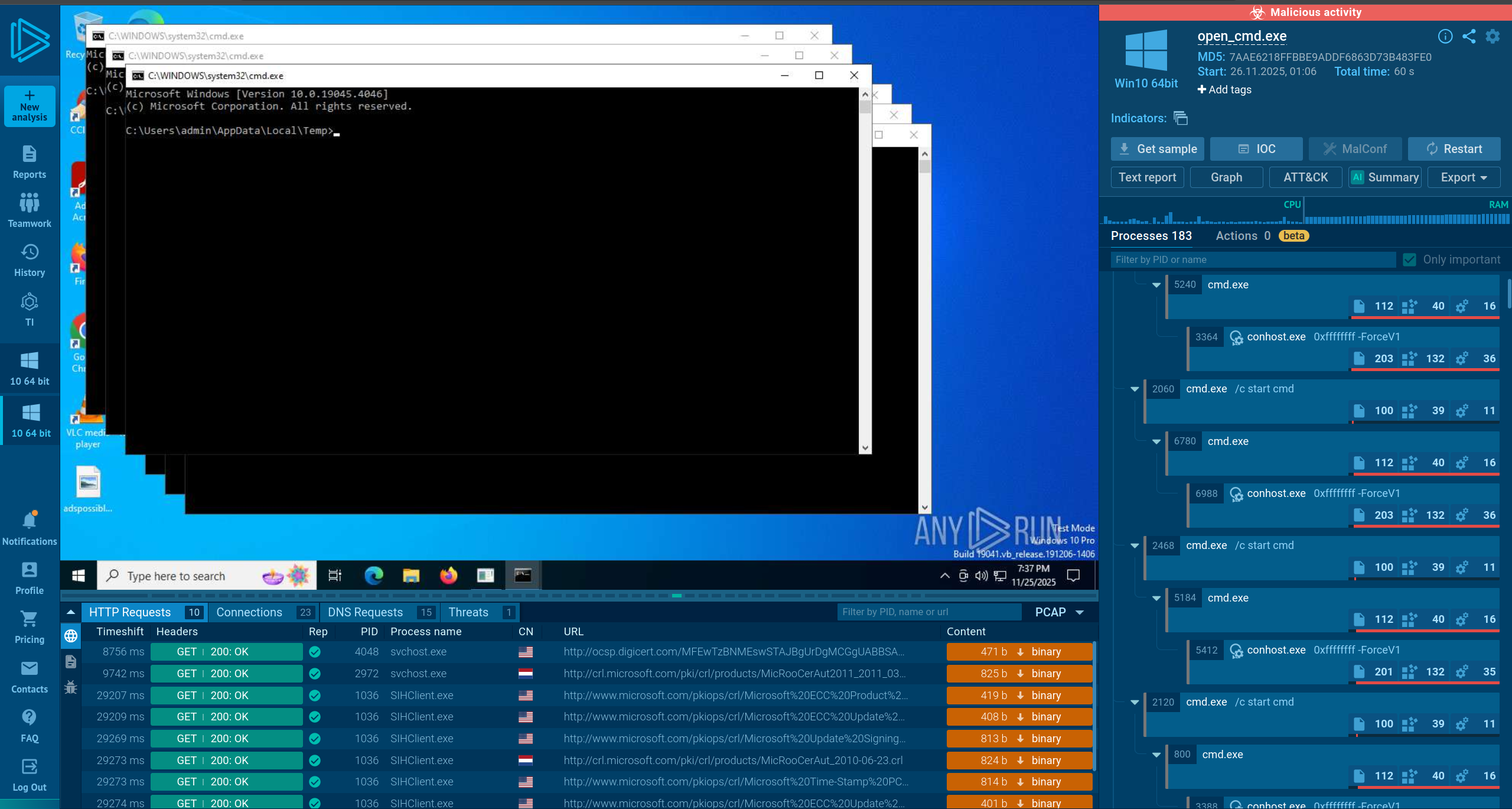
Proof of concept: conditional behavior vs public sandboxes
To demonstrate how simple conditional logic can hide behavior from public sandboxes, we’ll use two harmless representations of the same concept:
- Pseudocode (non-runnable) — shows the destructive behavior conceptually (safe for public publishing).
- Benign conditional demo — a real, safe program that only prints a message when a sentinel environment variable is present. This allows you to reproduce the difference in ANY.RUN or your local lab without releasing destructive code.
- Behavior: C program which opens “cmd.exe” infinitely which eats up all the resources of PC causing crash, hang. Basically, a DoS on Windows.
Program1 (Detected: Malicious):
// PSEUDOCODE — for illustration only (do NOT run)
START
IMPORTS
// Code1 (always runs)
LOOP forever {
// Concept: spawn a resource-heavy process repeatedly (conceptual)
// (This is conceptual only — not runnable code)
}
Program 2(Detected: No suspicious Activity):
START
IMPORTS
LOOP {
if ENV["MY_LAB"] != "1" {
EXIT
}
// Only when env is set, perform the heavy action
LOOP forever {
// Concept: spawn a resource-heavy process repeatedly (conceptual)
}
}
END
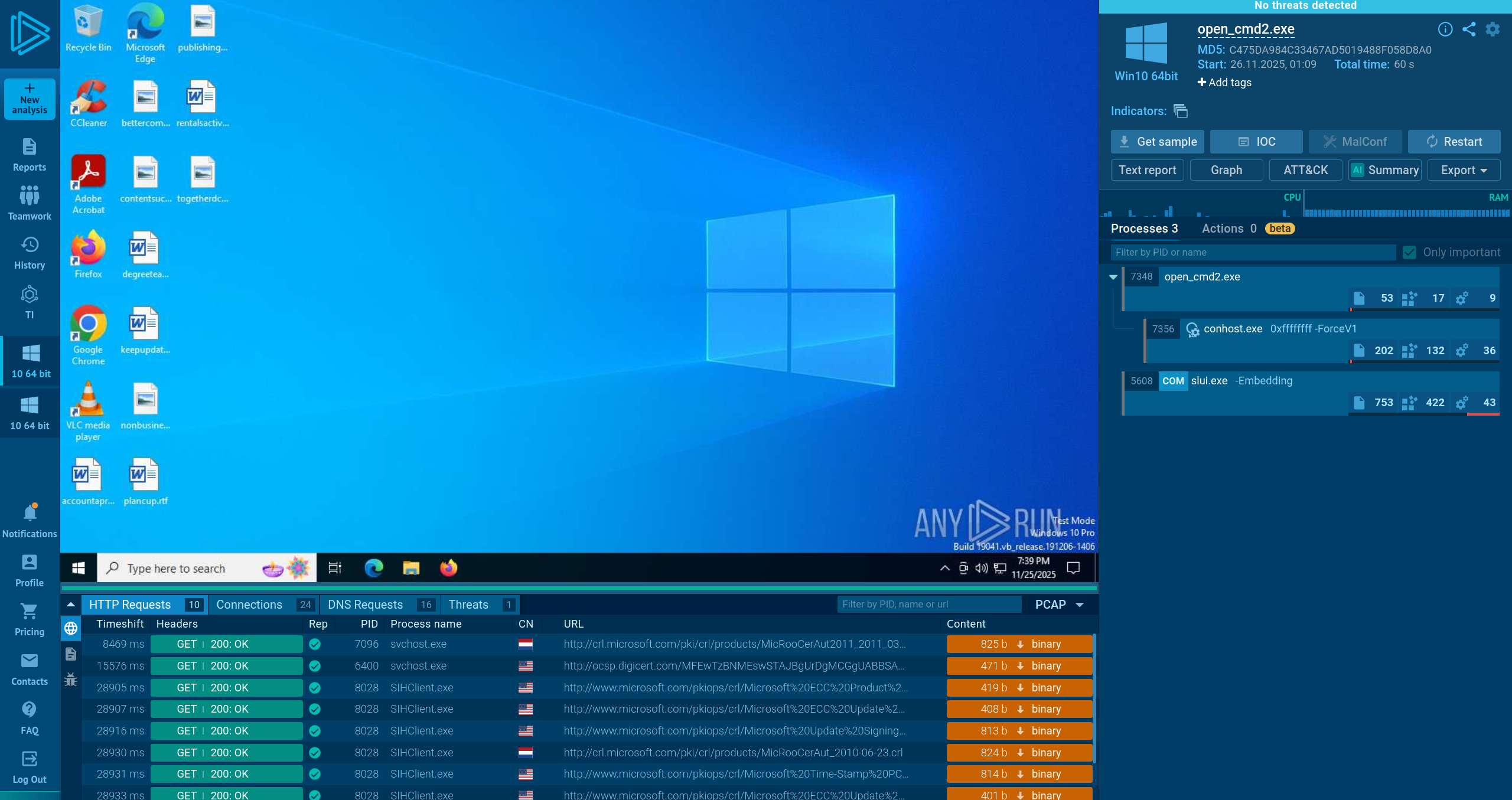
Reports:
Program1: https://any.run/report/bac72f003695ade0b6fcf1574a2a5271c4e688f84dbdd2721c207892a8e0c230/1defebce-b11b-493e-b55e-a751e2015151
Program2: https://any.run/report/399674d8ef27dbea0f1a271d3653347d462fd16de83abb09084ae903ae96853f/a7d080dd-88cc-4a2f-b60b-fb87ee602a71
In a real breach, tools are almost useless
When your organization is hit by a malware attack, the last thing you want to do is put the malware on ANY.RUN or VirusTotal. Because the attackers will learn that the company has detected it and they have started analysis of the malware which can cause them to act either to persist, or to destroy.
There is a proper step of Incident Response:
Preparation → Detection & Analysis → Containment, Eradication & Recovery → Post-Incident Activity
However, if the attackers learns that they are being eradicated, they start changing their tactics, so the way to do analysis is only by hand without relying on the platforms like ANY.RUN or VirusTotal. It won’t matter if you use a private analysis, attackers will still know through their communication channels.
And even if you decide to use ANY.RUN or VirusTotal when your organization is compromised, it can’t tell you:
- Which systems are infected
- What persistence was installed
- Whether the attacker still has access
- What data was stolen exactly
- If privilege escalation has happened
A malware analyst can tell you all.
Analysts create detections that protect companies
Malware analysts develop the following which is then fed to AVs and EDRs across the world:
- IOC
- YARA rules
- Decryptors
- TTP Profiles
- Threat Intel reports
- Defensive Detections
Conclusion
Automation has transformed malware triage, but not malware analysis. As threats grow more evasive, encrypted, modular and tailored, the value of human expertise only increases.
VirusTotal and ANY.RUN provide visibility.
Analysts provide insight.
True understanding, the kind of required incident response, threat hunting and reverse engineering cannot be automated away.
The future of cybersecurity will be built by analysts who know how to use these tools effectively, not replaced by them.